Microsoft Entra ID: Agent ID Administrator Role Abuse & Privilege Escalation
Security researchers have identified a critical flaw in Microsoft Entra ID (formerly Azure Active Directory) involving the Agent ID Administrator role. This vulnerability allows attackers to abuse this seemingly low-privilege role to escalate their permissions dramatically—hijacking service principals and potentially gaining full control over an organization's entire cloud tenant. This finding demands immediate attention from all organizations relying on Microsoft's identity and access management platform.
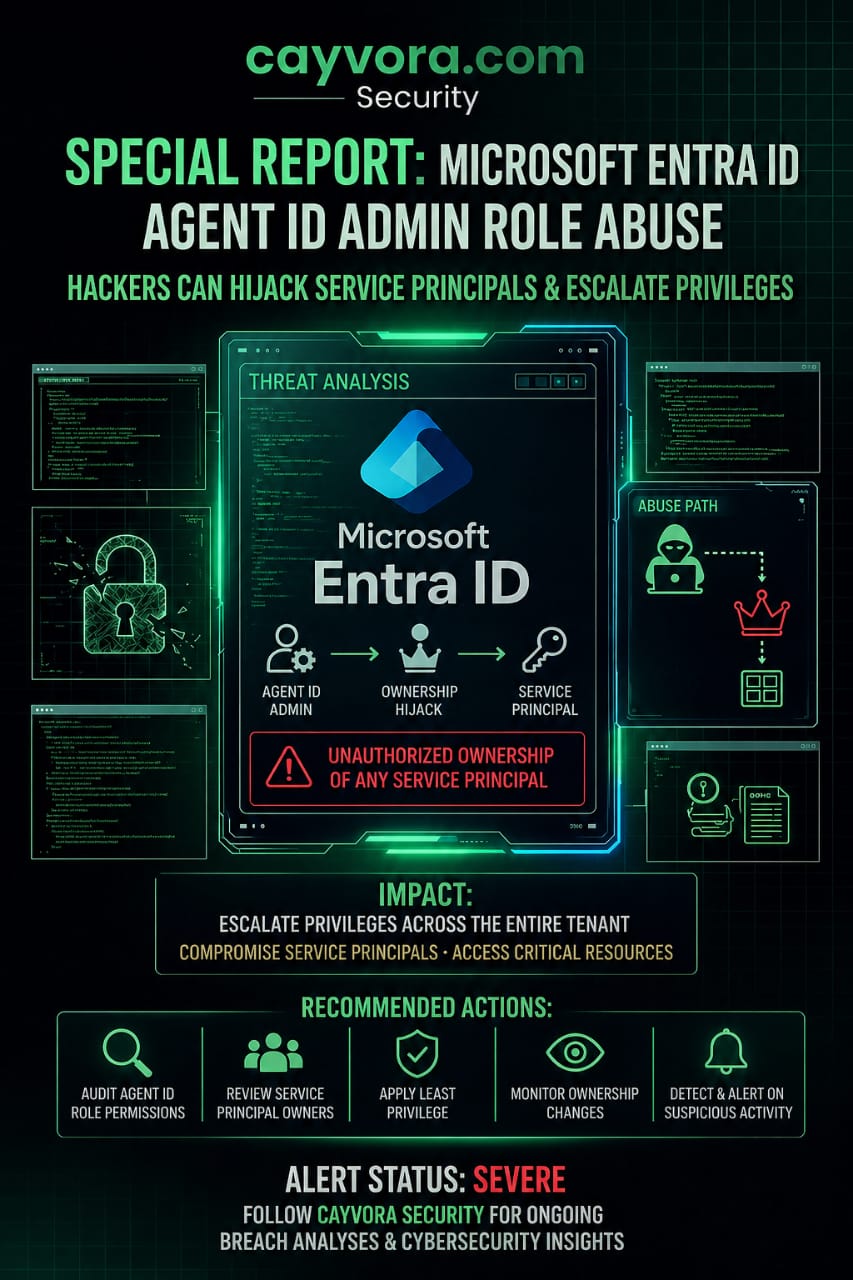
Alert Status: SEVERE — Attackers can escalate privileges across the entire tenant. Compromise service principals and access critical resources. Immediate IAM audit recommended.
Understanding the Vulnerability
What Is the Agent ID Administrator Role?
The Agent ID Administrator role in Microsoft Entra ID is designed to manage agent identities—machine identities used by automated services and agents within the Microsoft ecosystem. On the surface, this appears to be a narrowly scoped, low-privilege role intended for operational management tasks.
The Abuse Path
However, researchers discovered that the Agent ID Administrator role contains implicit permissions that extend far beyond its intended scope:
- Agent ID Admin → Ownership Hijack: A user with the Agent ID Administrator role can modify the ownership attributes of existing service principals. This means they can assign themselves as the owner of any service principal in the tenant.
- Ownership Hijack → Service Principal Control: As the owner of a service principal, the attacker gains the ability to modify its credentials (add new client secrets or certificates), change its permissions, and impersonate it for API calls.
- Service Principal Control → Tenant Compromise: Many service principals in enterprise environments have high-privilege permissions—including Global Administrator, Application Administrator, or Privileged Role Administrator. By hijacking a service principal with these permissions, the attacker effectively gains full administrative control over the entire Entra ID tenant.
Real-World Impact Scenario
Consider a typical corporate Azure environment:
- An IT helpdesk technician is granted the Agent ID Administrator role as part of their operational duties.
- The technician's account is compromised via a phishing attack.
- The attacker uses the compromised account to take ownership of a service principal that has Contributor-level access to the organization's Azure subscriptions.
- With this access, the attacker deploys cryptocurrency miners on the organization's virtual machines, exfiltrates data from Azure Storage accounts, and creates persistent backdoor accounts.
- Because the attack leveraged legitimate Entra ID role assignments, traditional security monitoring may not flag the activity as suspicious.
Recommended Defensive Actions
Organizations using Microsoft Entra ID should take the following steps immediately:
1. Audit Agent ID Role Assignments
- Review all users and groups assigned the Agent ID Administrator role in your Entra ID tenant.
- Remove the role from any accounts that do not have a documented, justified business need for it.
- Apply the Principle of Least Privilege (PoLP): no user should have more permissions than their job function requires.
2. Review Service Principal Owners
- Audit the ownership of all service principals in your tenant. Identify any unexpected or unauthorized owners.
- Use Microsoft Graph API or PowerShell to enumerate service principal ownership:
# List all service principals and their owners
Get-MgServicePrincipal -All | ForEach-Object {
$owners = Get-MgServicePrincipalOwner -ServicePrincipalId $_.Id
[PSCustomObject]@{
DisplayName = $_.DisplayName
AppId = $_.AppId
Owners = ($owners | ForEach-Object { $_.AdditionalProperties.userPrincipalName }) -join ', '
}
} | Export-Csv -Path "ServicePrincipalOwners.csv" -NoTypeInformation3. Implement Privileged Identity Management (PIM)
- Enable Azure AD Privileged Identity Management for all privileged roles, including Agent ID Administrator.
- Require just-in-time (JIT) activation with multi-factor authentication and business justification for all privileged role assignments.
- Set maximum activation durations (e.g., 4 hours) and require re-approval for extensions.
4. Monitor for Ownership Changes
- Configure Azure Monitor and Microsoft Sentinel to alert on service principal ownership changes.
- Create detection rules that trigger when a non-Global Administrator modifies service principal ownership or adds new credentials to a service principal.
5. Enforce Conditional Access Policies
- Apply Conditional Access policies that restrict privileged role usage to compliant, managed devices from trusted network locations.
- Block legacy authentication protocols that can bypass MFA requirements.
Implications for Moroccan Organizations
Many Moroccan enterprises and government entities are in the process of migrating to Microsoft 365 and Azure. This vulnerability has direct implications:
- Government Cloud Deployments: Moroccan public sector organizations using Microsoft 365 for Government must audit their Entra ID configurations to ensure that administrative roles are properly scoped and monitored.
- Financial Sector Compliance: Banks and financial institutions subject to Bank Al-Maghrib cybersecurity guidelines must demonstrate that their IAM controls prevent privilege escalation attacks.
- CNDP Data Protection: If a privilege escalation attack leads to unauthorized access to personal data, the organization faces CNDP compliance obligations including breach notification within 72 hours.
Conclusion
The Microsoft Entra ID Agent ID Administrator vulnerability is a textbook example of why identity is the new security perimeter. At Cayvora Security, we strongly recommend that all organizations using Microsoft cloud services conduct an immediate IAM audit focused on role assignments, service principal ownership, and privileged access management. Do not wait for Microsoft to patch this—implement the defensive controls outlined above today.