Uncovering WordPress Vulnerabilities: Stop Data Leaks & Brute-Force Attacks
During recent security audits, Cayvora has identified a recurring and critical pattern affecting numerous installations. This vulnerability exposes websites to significant risks through user enumeration and brute-force attacks. As leaders in Cybersecurity Morocco, we emphasize the importance of addressing these WordPress Security flaws immediately.
The Technical Flow: How the Attack Works
The attack begins with a common REST API endpoint configuration flaw. By default, the endpoint at /wp-json/wp/v2/users leaks sensitive information, including the exact administrative usernames. This is known as User Enumeration.
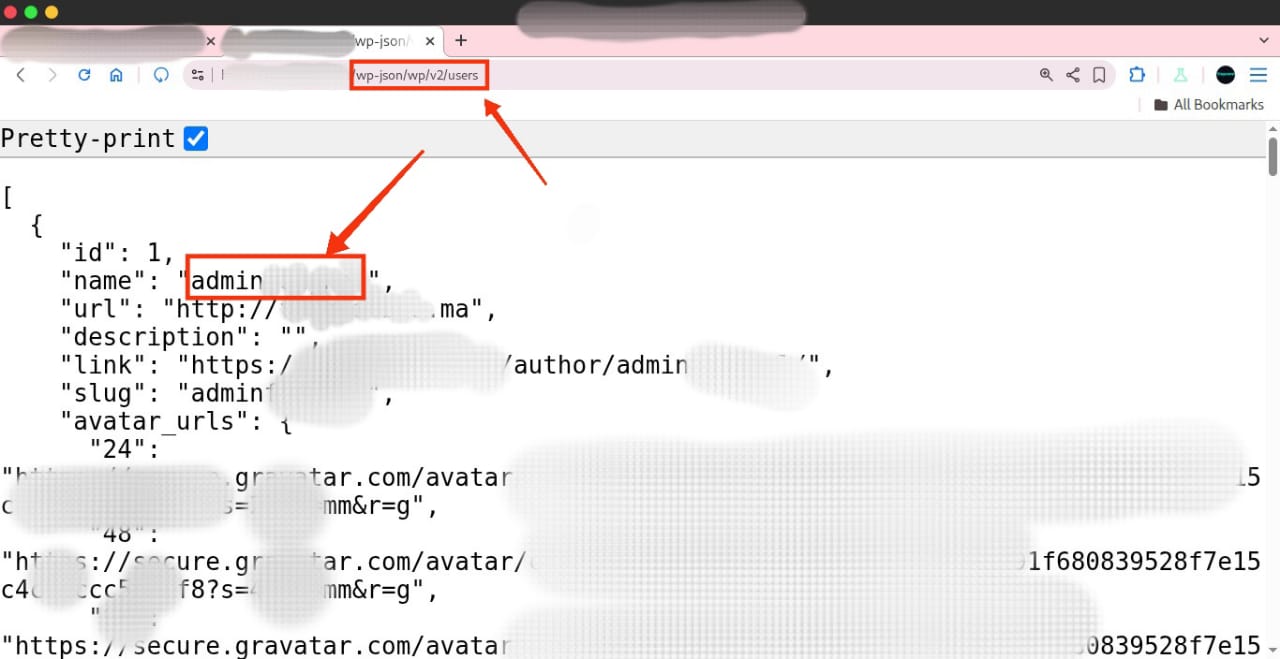
Demonstration of REST API information disclosure.
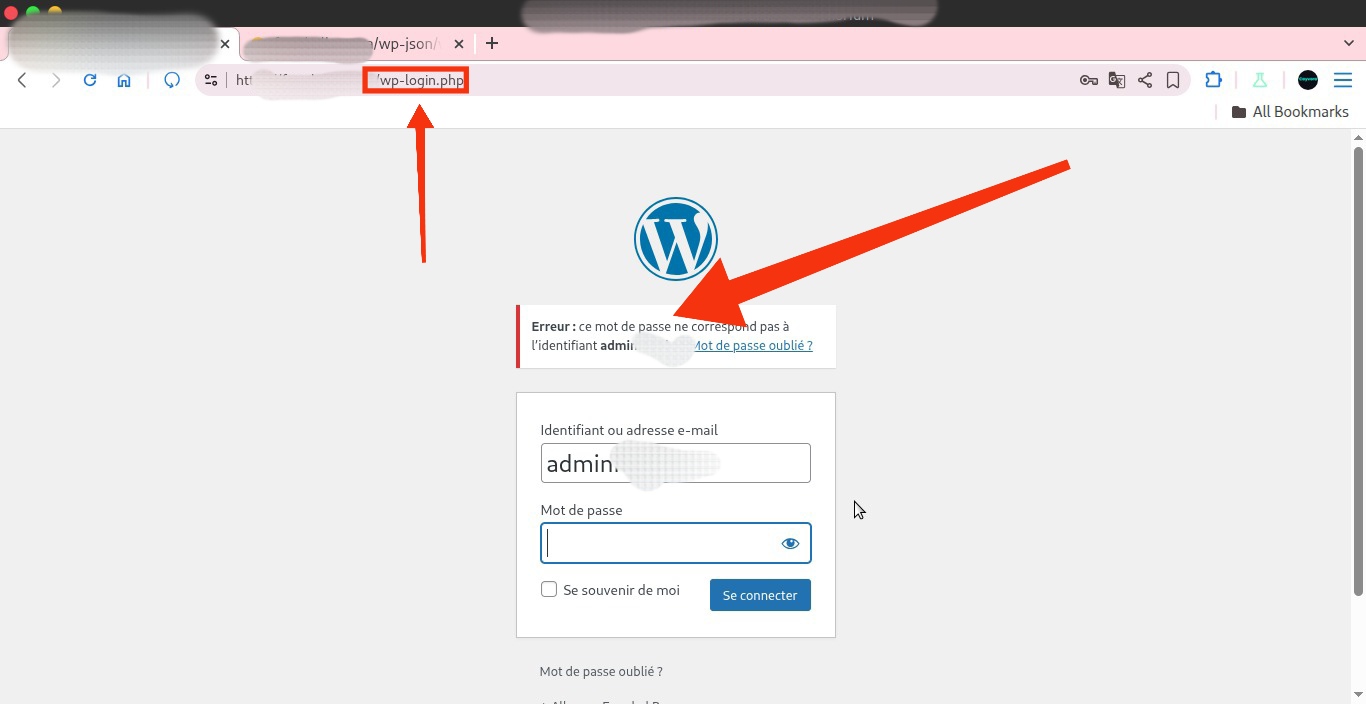
Once the attacker obtains the valid username, they move to the next phase: exploiting the login portal. Because many servers lack proper rate limiting on wp-login.php, attackers can launch automated brute-force attacks against the account without being blocked.
Demonstration of brute-force risk on wp-login.php.
The Impact of the Vulnerability
Knowing the admin username is "50% of the work" for an attacker. With half of the authentication equation handed to them on a silver platter, hackers only need to guess the password. Without rate limits, a weak password will inevitably be cracked, leading to a full site compromise, data breaches, and reputation damage.
Mitigation: 3 Steps to Secure Your Site
To eliminate this threat and ensure professional-grade PenTesting standards, follow these three clear mitigation steps:
- Disable the REST API (or Restrict It): If you do not need the WordPress REST API, disable it entirely. Alternatively, restrict access to the users endpoint for unauthenticated visitors.
- Implement Rate Limiting: Use a WAF (Web Application Firewall) or security plugin to enforce strict rate limiting on
wp-login.php, blocking IP addresses after repeated failed login attempts. - Enable Two-Factor Authentication (2FA): Require 2FA for all administrative accounts. Even if an attacker guesses the password, they cannot access the dashboard without the second factor.
Secure Your Infrastructure Today
Don't wait for a breach to realize your site is vulnerable. Contact Cayvora today for a comprehensive security audit and protect your business against modern cyber threats.